So, you’re all happy about that “smart” new toaster oven you got for Christmas. Combining heating elements, sensors and smartphone technology, it’s a computer that cooks, basically.
Why, it even has a chipset with a quad-core processor paired with a 5-inch touchscreen and an embedded HD camera that keeps “an eye” on the food while it cooks. Just dial up the image on your smart phone while you lounge poolside.
Such high-tech living is all part of the growing, ineluctable, trend toward realizing the Internet of Things (IoT), a movement that Jeremy Khan sees as controlling “everything from factory equipment to traffic lights and household appliances through the Web, creates vast opportunities for improved efficiency and convenience.”
Neat, eh? But Khan offers words of caution: that smart toaster oven may also represent a neat opportunity for cyber thieves to hack into your personal, web-connected domain.
Seriously.
“Hijacking smart toasters and refrigerators and hacking corporate ventilation systems are among the new threats envisioned by cybersecurity experts as an increasing array of items are connected to the Internet,” Kahn writes.
"And unless companies address the emerging cybersecurity risks the IoT poses, the IoT will fail," Stephen Pattison, the vice president of public affairs at ARM Holdings Plc, told Khan.
“We ain’t seen nothing yet," added Pattison, speaking at the Security Innovation Network’s U.S./U.K. Global Cybersecurity Innovation Summit in London last month.
THE INTERNET OF THINGS. WHAT IS IT, EXACTLY?
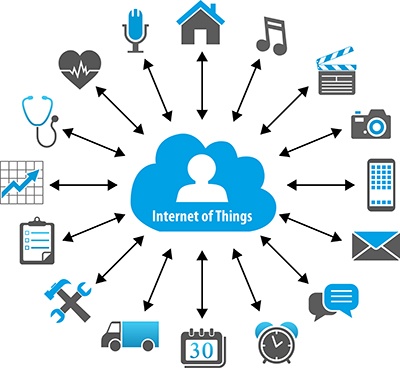
The Internet of Things is a system composed of one or more devices (or components) that gather data about a condition or an event. That’s the most basic definition,
according to BCC Research analyst Anand Joshi.
“These devices could have one or more sensors gathering information. Each one is connected to the Internet via a direct connection, such as a cellular Internet connection, or an indirect connection, such as a Bluetooth interface to a tablet or smartphone that is connected to the Internet directly or via a networking hub. These devices may also talk to a hub or network router that provides Internet connectivity within a home.”
Joshi further explains: “Using similar technology, the devices could also be connected to each other, allowing them to gather and act on data that they receive as well as data that they send. A Web interface is commonly used to communicate to these devices, although some devices have on-screen interfaces. There may be one or more applications in the cloud receiving data from these devices. The applications process the data to produce IoT devices in some instances may also have actuation capabilities, meaning they can take an action. An example of this would be a device that senses the presence or absence of people around the house, turns a lock on or off, allows remote control of the lock via a smartphone. Or, as with a smart toaster, keep you posted remotely on the cooking status of your food.”
Although experts coined the phrase “Internet of Technology” to establish the universal electronic product code using radio frequency identification (RFID) systems, the many applications and industries enabled by IT networks with integrated components is quickly redefining IoT beyond RFID, machine-to-machine (M2M) or any previous point interconnection technology. IoT encompasses all of these and through the Internet, mobile devices and data analytics, new layers of capability are constantly being added.
And those new advancements bring substantial security challenges.
IOT SECURITY ISSUES AND CHALLENGES
Internet technologies are developing at seeming warp speed, prompting critics to argue that appropriate consideration of the profound security challenges is lacking. They also want to debate the regulatory changes that might be necessary, says Joshi.
“As the IoT grows, cyberattacks are likely to become increasingly physical (rather than simply virtual) threats. Computer-controlled devices in automobiles, such as brakes, locks, hood releases, horn, heat, dashboard, and even the engine itself, have been shown to be vulnerable to attackers who have access to the onboard network,” he says. “There are already reports that IoT devices such as baby monitors are an easy hack. Hackers can gain access to user’s wireless network via such devices making the data on any computer connected to the network vulnerable.”
WILD WEST
National security agencies have focused mostly on the risk to critical infrastructure from Internet-enabled industrial control systems, such as those that operate nuclear power plants or chemical factories, Alison Vincent, chief technology officer for Ciscos in U.K. and Ireland, told Kahn. As a result, many of these networks have already been fortified against possible cyberattacks.
In terms of privacy and data protection, consumer devices pose the greater risk. “Consumer technology is the Wild West,” Vincent said.
Paddy Francis warned of the risks posed by increasingly Internet-connect household appliances. Francis, chief technology officer for Airbus Group SEs Defense and Space division, told Khan that the sheer number of these appliances--from coffee makers to refrigerators to televisions--and the relatively weak firewalls of most household wireless networks, could make such mundane items attractive to cybercriminals for use as ‘botnets’ in so-called denial of service attacks, in which a hacker disables a website by flooding it with specious message traffic.”
Francis also worried about he termed “ cyber assisted burglary,” which involves criminals planning home invasions by “hacking into household networks to extract data from routine items” such as smart lighting or heating systems to determine when the house was unoccupied.
CONSTANT UPDATING
Even something as apparently harmless as allowing a building facilities team to control the heating and air conditioning systems via a mobile phone app that uses IoT technology poses a potential risk. Jeremy Watson, vice dean of engineering sciences at University College London, used the example of “a disgruntled employee with access to the system might use it to cause temperatures in a server room to soar, resulting in computer failure.”
Even Internet-enabled devices with sound security measures remain at potential risk as technology evolves seemingly in lockstep with the tactics of hackers and cyber criminals.
Welcome to the Age of the Internet. Strap yourselves in, it’s going to be a bumpy, but interesting, ride.
The total market for IoT devices and chipsets is expected to reach almost $4.2 billion and $49.2 billion in 2014 and 2020, respectively, reflecting a six-year annual compound growth rate (CAGR) of 49.3%. IoT devices are expected to account for a major portion of this growth, growing from $4 billion in 2014 to about $48.4 billion in 2020. The IoT chipset industry should demonstrate a six-year CAGR of 36.3%.